AAA Config Huawei OLT by HWTACACS protocol:
Today i will show how to configure AAA in Huawei OLT by using HWTACACS protocol. [boxads]
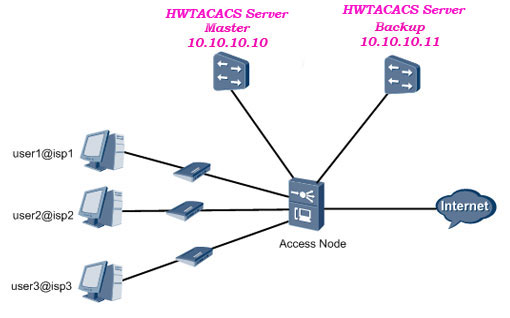
Service Requirements:
- The HWTACACS server performs authentication, authorization, and accounting for 802.1X access users.
- The user logs in to the server carrying the domain name.
- The HWTACACS server with the IP address 10.10.10.10 functions as the primary server for authentication, authorization, and accounting.
- The HWTACACS server with the IP address 10.10.10.11 functions as the secondary server for authentication, authorization, and accounting.
- Other parameters adopt the default settings.
Technology Diagram:
Procedure:
Step 1: Configure the AAA authentication scheme.
-The authentication scheme specifies how all the users in an ISP1 domain are authenticated.
-The system supports up to 16 authentication schemes. The system has a default authentication
scheme named default. It can be modified, but cannot be deleted.
- 1. Run the aaa command to enter the AAA mode.
- 2. Run the authentication-scheme command to add an authentication scheme.
- 3. Run the authentication-mode local command to configure the authentication mode of the authentication scheme. Use the HWTACACS protocol to authenticate users.
- 4. Run the quit command to return to the AAA mode.
[bodyads]
Configuration Example of authentication scheme:
Configure authentication scheme named newscheme (users are authenticated through HWTACACS).
Huawei-OLT(config)#aaa
Huawei-OLT(config-aaa)#authentication-scheme newscheme
Huawei-OLT(config-aaa-authen-newscheme)#authentication-mode hwtacacs
Huawei-OLT(config-aaa-authen-newscheme)#quit
Step 2: Configure the AAA authorization scheme.
-The authorization scheme specifies how all the users in an ISP1 domain are authorized.
- 1. In the AAA mode, run the authorization-scheme command to add an AAA authorization scheme.
- 2. Run the authorization-mode hwtacacs command to configure the authorization mode.
- 3. Run the quit command to return to the AAA mode.
- 4. Run the quit command to return to the global config mode.
Configuration Example of authorization scheme:
Configure authorization scheme named newscheme (users are authorized through HWTACACS).
Huawei-OLT(config-aaa)#authorization-scheme newscheme
Huawei-OLT(config-aaa-author-newscheme)#authorization-mode hwtacacs
Huawei-OLT(config-aaa-author-newscheme)#quit
Step 3: Configure the AAA accounting scheme.
-The accounting scheme specifies how all the users in an ISP1 domain are charged.
-The system supports up to 128 accounting schemes. The system has a default accounting scheme named default. It can be modified, but cannot be deleted.
- 1. In the AAA mode, run the accounting-scheme command to add an AAA accounting scheme.
- 2. Run the accounting-mode hwtacacs command to configure the accounting mode. By default, the accounting is not performed.
- 3. Run the accounting interim interval command to set the interval of real-time accounting.
By default, the interval is 0 minutes, that is, the real-time accounting is not performed.
4. Run the quit command to return to the AAA mode.
Configuration Example of accounting scheme:
Configure accounting scheme named newscheme (users are authenticated through HWTACACS). the interval is 10 minutes.
Huawei-OLT(config-aaa)#accounting-scheme newscheme
Huawei-OLT(config-aaa-accounting-newscheme)#accounting-mode hwtacacs
Huawei-OLT(config-aaa-accounting-newscheme)#accounting interim interval 10
Huawei-OLT(config-aaa-accounting-newscheme)#quit
Huawei-OLT(config-aaa)#quit
Step 4: Configure the HWTACACS protocol.
-The configuration of the HWTACACS protocol of the MA5600T/MA5603T/MA5608T is on the basis of the HWTACACS server group.
-In actual networking scenarios, an HWTACACS server group can be an independent HWTACACS server or a combination of two HWTACACS servers, that is, a primary server and a secondary server with the same configuration but different IP addresses.
-Each HWTACACS server template contains the primary/secondary server IP address, shared key, and HWTACACS server type.
-Primary and secondary authentication, accounting, and authorization servers can be configured. The IP address of the primary server, however, must be different from that of the secondary server. Otherwise, the configuration of primary and secondary servers will fail.
By default, the IP addresses of the primary and secondary servers are both 0.0.0.0.
- 1. Run the hwtacacs-server template command to create an HWTACACS server template and enter the HWTACACS server template mode.
- 2. Run the hwtacacs-server authentication command to configure a primary authentication server. You can select secondary to configure a secondary authentication server.
- 3. Run the hwtacacs-server authorization command to configure a primary authorization server. You can select secondary to configure a secondary authorization server.
- 4. Run the hwtacacs-server accounting command to configure a primary accounting server. You can select secondary to configure a secondary accounting server.
- 5. (Optional) Run the hwtacacs-server shared-key command to configure the shared key of the HWTACACS server
- 6. (Optional) Run the hwtacacs-server timer response-timeout to set the response timeout time of the HWTACACS server.
- 7. (Optional) In the global config mode, run the hwtacacs-server accounting-stop-packet command to configure the re-transmission mechanism of the accounting-stop packets of the HWTACACS server.
- 8. (Optional) Run the (undo)hwtacacs-server user-name domain-included command to configure the user name (not) to carry the domain name when transmitted to the HWTACACS server.
- 9. Run the quit command to return to the global config mode.
Configuration Example of HWTACACS protocol:
Huawei-OLT(config)#hwtacacs-server template hwtest
Create a new HWTACACS-server template
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authentication 10.10.10.10
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authentication 10.10.10.11 secondary
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authorization 10.10.10.10
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authorization 10.10.10.11 secondary
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server accounting 10.10.10.10
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server accounting 10.10.10.11 secondary
Huawei-OLT(config-hwtacacs-hwtest)#quit
[bodyads]
Step 5: Configure the 802.1X authentication.
- 1. Enable the 802.1X global switch. Enable the 802.1X authentication for ports 1, 2, and 3. The 802.1X needs to be triggered by DHCP. Therefore, the DHCP-trigger authentication must be enabled.
Huawei-OLT(config)#dot1x enable
Huawei-OLT(config)#dot1x service-port 1
Huawei-OLT(config)#dot1x service-port 2
Huawei-OLT(config)#dot1x service-port 3
Huawei-OLT(config)#dot1x dhcp-trigger enable
- 2. Configure an 802.1X parameters. In the local termination authentication, the 802.1X parameters should be configured to be in the EAP termination mode. The count of allowed handshake failure is 1 and the handshake interval is 20s.
Huawei-OLT(config)#dot1x keepalive retransmit 1 interval 20 service-port 1
Huawei-OLT(config)#dot1x keepalive retransmit 1 interval 20 service-port 2
Huawei-OLT(config)#dot1x keepalive retransmit 1 interval 20 service-port 3
Huawei-OLT(config)#dot1x eap-end service-port 1
Huawei-OLT(config)#dot1x eap-end service-port 2
Huawei-OLT(config)#dot1x eap-end service-port 3
Step 6: Create a domain.
A domain is a group of users of the same type.
-In the user name format userid@domain-name (for example, Shahed@huawei.net),”userid” indicates the user name for authentication and “domain-name” followed by “@” indicates the domain name.
-The domain name for user login cannot exceed 15 characters, and the other domain names cannot exceed 20 characters.
- 1. Run the aaa command to enter the AAA mode.
- 2. In the AAA mode, run the domain command to create a domain.
Configuration Example of domain Create:
Create a domain named isp1.
Huawei-OLT(config)#aaa
Huawei-OLT(config-aaa)#domain isp1
Info: Create a new domain
Step 7: Use the authentication scheme.
-You can use an authentication scheme in a domain only after the authentication scheme is created.
-In the domain mode, run the authentication-scheme command to use the authentication scheme.
Configuration Example of Use the authentication scheme:
Huawei-OLT(config-aaa-domain-isp1)#authentication-scheme newscheme
Step 8: Use the authorization scheme.
-You can use an authorization scheme in a domain only after the authorization scheme is created.
-In the domain mode, run the authorization-mode command to use the authorization scheme.
Configuration Example of Use the authorization scheme:
Huawei-OLT(config-aaa-domain-isp1)#authorization-scheme newscheme
Step 9: Use the accounting scheme.
-You can use an accounting scheme in a domain only after the accounting scheme is created.
-In the domain mode, run the accounting-scheme command to use the accounting scheme.
Configuration Example of Use the accounting scheme:
Huawei-OLT(config-aaa-domain-isp1)#accounting-scheme newscheme
Step 10: Use the HWTACACS server template.
-You can use an HWTACACS server template in a domain only after the HWTACACS server template is created.
- 1. In the domain mode, run the hwtacacs-server command to use the HWTACACS server template.
- 2. Run the quit command to return to the AAA mode.
Configuration Example of Bind the HWTACACS server template:
Huawei-OLT(config-aaa-domain-isp1)#hwtacacs-server hwtest
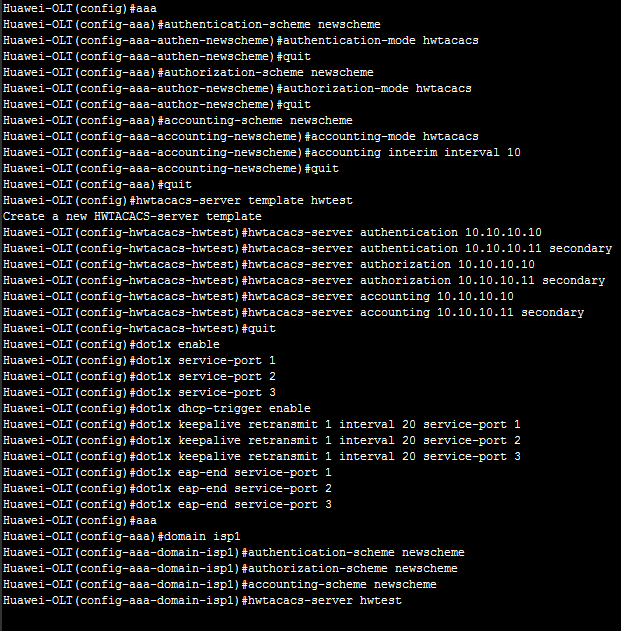
Example of full AAA Config Huawei OLT:
Huawei-OLT(config)#aaa
Huawei-OLT(config-aaa)#authentication-scheme newscheme
Huawei-OLT(config-aaa-authen-newscheme)#authentication-mode hwtacacs
Huawei-OLT(config-aaa-authen-newscheme)#quit
Huawei-OLT(config-aaa)#authorization-scheme newscheme
Huawei-OLT(config-aaa-author-newscheme)#authorization-mode hwtacacs
Huawei-OLT(config-aaa-author-newscheme)#quit
Huawei-OLT(config-aaa)#accounting-scheme newscheme
Huawei-OLT(config-aaa-accounting-newscheme)#accounting-mode hwtacacs
Huawei-OLT(config-aaa-accounting-newscheme)#accounting interim interval 10
Huawei-OLT(config-aaa-accounting-newscheme)#quit
Huawei-OLT(config-aaa)#quit
Huawei-OLT(config)#hwtacacs-server template hwtest
Create a new HWTACACS-server template
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authentication 10.10.10.10
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authentication 10.10.10.11 secondary
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authorization 10.10.10.10
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server authorization 10.10.10.11 secondary
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server accounting 10.10.10.10
Huawei-OLT(config-hwtacacs-hwtest)#hwtacacs-server accounting 10.10.10.11 secondary
Huawei-OLT(config-hwtacacs-hwtest)#quit
[adsense]
Huawei-OLT(config)#dot1x enable
Huawei-OLT(config)#dot1x service-port 1
Huawei-OLT(config)#dot1x service-port 2
Huawei-OLT(config)#dot1x service-port 3
Huawei-OLT(config)#dot1x dhcp-trigger enable
Huawei-OLT(config)#dot1x keepalive retransmit 1 interval 20 service-port 1
Huawei-OLT(config)#dot1x keepalive retransmit 1 interval 20 service-port 2
Huawei-OLT(config)#dot1x keepalive retransmit 1 interval 20 service-port 3
Huawei-OLT(config)#dot1x eap-end service-port 1
Huawei-OLT(config)#dot1x eap-end service-port 2
Huawei-OLT(config)#dot1x eap-end service-port 3
Huawei-OLT(config)#aaa
Huawei-OLT(config-aaa)#domain isp1
Huawei-OLT(config-aaa-domain-isp1)#authentication-scheme newscheme
Huawei-OLT(config-aaa-domain-isp1)#authorization-scheme newscheme
Huawei-OLT(config-aaa-domain-isp1)#accounting-scheme newscheme
Huawei-OLT(config-aaa-domain-isp1)#hwtacacs-server hwtest
Look like bellow format in OLT: