Cisco Switch VLAN Security
Today I will discuss about Cisco Switch VLAN Security issue. A Virtual Local Area Network (VLAN) is a broadcast domain. All members of a VLAN receive every broadcast packet sent by members of the same VLAN, but they do not receive packets sent by members of a different VLAN. All members of a VLAN are grouped logically into the same broadcast domain independent of their physical location. Adding, moving or changing members is achieved via software within a switch. Routing is required for communication among members of different VLANs.[boxads]
The next subsections describe the vulnerabilities and corresponding counter measures for the following areas: VLAN 1, Private VLAN, VTP, Trunk Auto-Negotiation, VLAN Hopping and Dynamic VLAN Assignment.
- 1. VLAN1
Cisco switches use VLAN 1 as the default VLAN to assign to their ports, including their management ports. Additionally, Layer 2 protocols, such as CDP and VTP, need to be sent on a specific VLAN on trunk links, so VLAN 1 was selected. In some cases, VLAN 1 may span the entire network if not appropriately pruned. It also provides attackers easier access and extended reach for their attacks.
Do not use VLAN 1 for either out-of-band management or in-band management.
To provide out-of-band management that separates management traffic from user traffic, use the following VLAN Security commands as an example.
Create the out-of-band management VLAN.
Switch(config)# vlan 6
Switch(config-vlan)# name ADMINISTRATION-VLAN
Create a management IP address and restrict access to it. Also, enable the interface.
Switch(config)# no access-list 10
Switch(config)# access-list 10 permit 10.1.6.1
Switch(config)# access-list 10 permit 10.1.6.2
Switch(config)# interface vlan 6
Switch(config-if)# description ADMIN-VLAN
Switch(config-if)# ip address 10.1.6.121 255.255.255.0
Switch(config-if)# ip access-group 10 in
Switch(config-if)# no shutdown
Assign the management VLAN to the dedicated interface.
Switch(config)# interface fastethernet 4/1
Switch(config-if)# description Out-Of-Band Admin
Switch(config-if)# switchport mode access
Switch(config-if)# switchport access vlan 6
Switch(config-if)# no shutdown
Ensure all trunk ports will not carry the management VLAN (e.g., 6).
Switch(config)# interface range gigabitethernet 6/15 – 16
Switch(config-if)# switchport trunk allowed vlan remove 6
Assigned the following name for VLAN 1.
Switch# vlan 1
Switch(vlan)# name *** DEFAULT VLAN – Do NOT Use! ***
Assign all inactive interfaces to an unused VLAN other than VLAN 1 and shut down these interfaces. Note that unused VLANs are not routable.
Switch# vlan 999
Switch(vlan)# name *** BIT BUCKET for unused ports ***
Switch(vlan)# shutdown
Switch(vlan)# exit
Switch(config)# interface range fastethernet 5/45 – 48
Switch(config-if)# switchport mode access
Switch(config-if)# switchport access vlan 999
Switch(config-if)# shutdown
Assign all interfaces to VLANs other than VLAN 1.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport mode access
Switch(config-if)# switchport access vlan 999
- 2. Private VLAN (PVLAN)
In certain instances where similar systems do not need to interact directly, PVLANs provide additional protection. A primary PVLAN defines the broadcast domain with which the secondary PVLANs are associated. The secondary PVLANs may either be isolated PVLANs or community PVLANs. Hosts on isolated PVLANs communicate only with promiscuous ports, and hosts on community PVLANs communicate only among themselves and with associated promiscuous ports. This configuration provides fine-grained Layer 2 isolation control for each system.
A configuration with multiple servers on a single VLAN should use PVLANs for Layer 2 separation among the servers. Routers should be on promiscuous ports and servers on an isolated PVLAN. Only servers that need to communicate directly with other servers should be on a community PVLAN. Implement VACLs on the primary PVLAN to filter traffic originated by and routed to the same segment.[adsense]
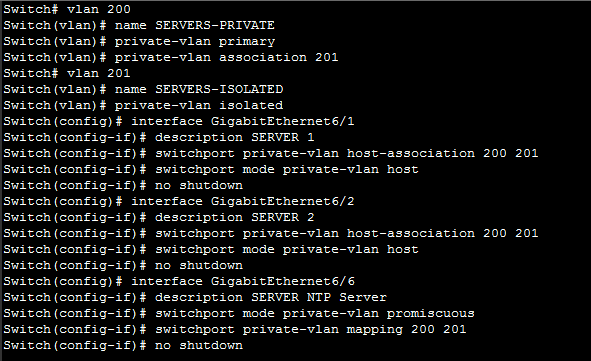
The following VLAN Security example creates a PVLAN with an NTP server on a promiscuous port and two isolated servers.
Switch# vlan 200
Switch(vlan)# name SERVERS-PRIVATE
Switch(vlan)# private-vlan primary
Switch(vlan)# private-vlan association 201
Switch# vlan 201
Switch(vlan)# name SERVERS-ISOLATED
Switch(vlan)# private-vlan isolated
Switch(config)# interface GigabitEthernet6/1
Switch(config-if)# description SERVER 1
Switch(config-if)# switchport private-vlan host-association 200 201
Switch(config-if)# switchport mode private-vlan host
Switch(config-if)# no shutdown
Switch(config)# interface GigabitEthernet6/2
Switch(config-if)# description SERVER 2
Switch(config-if)# switchport private-vlan host-association 200 201
Switch(config-if)# switchport mode private-vlan host
Switch(config-if)# no shutdown
Switch(config)# interface GigabitEthernet6/6
Switch(config-if)# description SERVER NTP Server
Switch(config-if)# switchport mode private-vlan promiscuous
Switch(config-if)# switchport private-vlan mapping 200 201
Switch(config-if)# no shutdown
- 3. Virtual Trunking Protocol (VTP)
VTP is a Cisco-proprietary Layer 2 messaging protocol used to distribute VLAN configuration information over trunks. VTP allows the addition, deletion and renaming of VLANs on a network-wide basis, which allows switches to have a consistent VLAN configuration within a VTP management domain. All switches in the same management domain share their VLAN information, and a switch may participate in only one VTP management domain.
A switch may be in one of three VTP modes: server, transparent and client.
By default, switches share VLAN information without any authentication. Thus, inaccurate VLAN settings can propagate throughout a VTP domain. Compounding this problem, switches come with VTP in server mode by default, and a server with a higher configuration revision number in its VTP database supersedes one with a lower number. It is entirely possible for a single switch, which has undergone a sufficient number of VTP re-configurations, to completely overwrite or eliminate all VLAN assignments of an operational network by just connecting it to the network. Such an attack would not necessarily have to be malicious; simply moving a lab switch to an operational network could have this effect.
It is clear that VTP simplifies administration, particularly where large numbers of VLANs are deployed. Nevertheless, VTP is sufficiently dangerous that its use is discouraged. If possible, turn off VTP by using the following commands.
Switch(config)# no vtp mode
Switch(config)# no vtp password
Switch(config)# no vtp pruning
If VTP is necessary, then consider the following settings. Set up VTP management domains appropriately. All switches in the same management domain share their VLAN information. A switch can only participate in one VTP management domain. Use the following command as an example to set the VTP management domain.
Switch(config)# vtp domain test.lab
Assign a strong password to the VTP management domain. All switches within the domain must be assigned the same password. This prevents unauthorized switches from adding themselves to the VTP management domain and passing incorrect VLAN information. Use password protection on VTP domains as shown in the command in the following example.
Switch(config)# vtp password g00d-P5WD
Enable VTP pruning and use it on appropriate ports. By default, VLANs numbered 2 through 1000 are pruning-eligible.
Switch(config)# vtp pruning
Set VTP to transparent mode with the following command.
Switch(config)# vtp transparent
- 4. Trunk Auto-Negotiation
A trunk is a point-to-point link between two ports, typically on different network systems, that aggregates packets from multiple VLANs. Cisco implements two types of trunks: IEEE 802.1q, which is an open standard; and ISL, which is a Cisco proprietary standard.
A port may use the Dynamic Trunking Protocol (DTP) to automatically negotiate which trunking protocol it will use, and how the trunking protocol will operate. By default, a Cisco Ethernet port’s default DTP mode is “dynamic desirable”, which allows the port to actively attempt to convert the link into a trunk. Even worse, the member VLANs of the new trunk are all the available VLANs on the switch. If a neighboring port’s DTP mode becomes “trunk”, “dynamic auto”, or “dynamic desirable”, and if the two switches support a common trunking protocol, then the line will become a trunk automatically, giving each switch full access to all VLANs on the neighboring switch. An attacker who can exploit DTP may be able to obtain useful information from these VLANs. [bodyads]
Do not use DTP if possible.
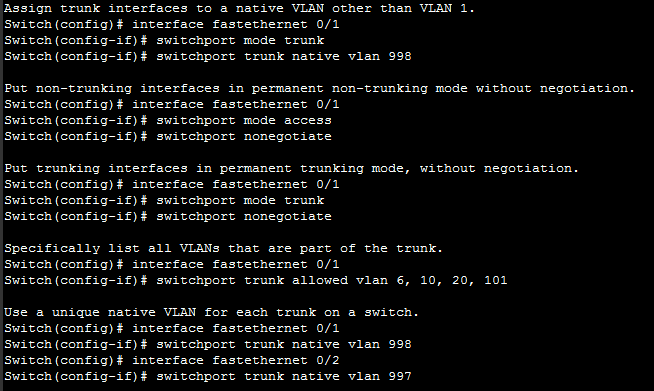
Assign trunk interfaces to a native VLAN other than VLAN 1.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport mode trunk
Switch(config-if)# switchport trunk native vlan 998
Put non-trunking interfaces in permanent non-trunking mode without negotiation.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport mode access
Switch(config-if)# switchport nonegotiate
Put trunking interfaces in permanent trunking mode, without negotiation.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport mode trunk
Switch(config-if)# switchport nonegotiate
Specifically list all VLANs that are part of the trunk.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport trunk allowed vlan 6, 10, 20, 101
Use a unique native VLAN for each trunk on a switch.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport trunk native vlan 998
Switch(config)# interface fastethernet 0/2
Switch(config-if)# switchport trunk native vlan 997
- 5. VLAN Hopping
In certain situations it is possible to craft a packet in such a way that a port in trunking mode will interpret a native VLAN packet as though it were from another VLAN, allowing the packet to become a member of a different VLAN. This technique is known as VLAN hopping. Using VLAN hopping, a malicious intruder who has access to one local network might inject packets into another local network in order to attack machines on the target network.
Disable CDP, VTP and DTP on each switch if possible. Assign a shutdown VLAN as the ‘native’ VLAN of each of the trunks, and do not use this VLAN for any other purpose.
Switch(config)# interface fastethernet 0/1
Switch(config-if)# switchport trunk native vlan 998
Switch(config-if)# no cdp enable
Restrict the VLANs on a trunk to only those that are necessary for that trunk, as described in the Trunk Auto-Negotiation subsection previously.