Virtual Routing and Forwarding basics (VRF):
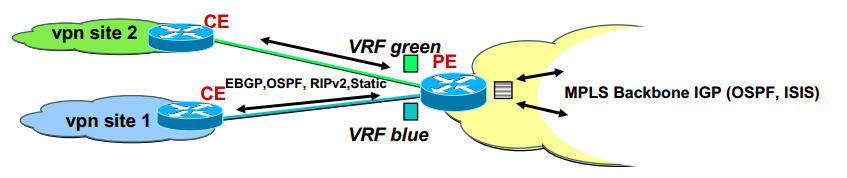
Today i will discuss about Virtual Routing and Forwarding basics (VRF). VRF is a Layer 3 VPN technique. VRF can be use with or without MPLS. If we look bellow diagram we see here two VRF one is green VRF and another is blue VRF. [boxads]
Virtual Routing and Forwarding basics (VRF) Diagram:
Now one question what is VRF ?
- VRF associates to one or more interfaces on PE.
- Privatize an interface. [i.e. coloring of the interface in diagram]
- Has its own routing table and forwarding table (CEF)
- VRF has its own instance for the routing protocol (static ,RIP,BGP,EIGRP,OSPF)
- CE router runs standard routing software
- PE installs the routes, learned from CE routers, in the appropriate VRF routing table(s)
- Also PE installs the IGP (backbone) routes in the global routing table
- VPN customers can use overlapping IP addresses.
[adsense]
Introduction of VRF:
Virtual Routing and Forwarding Table (VRF) allows to create multiple routing tables within a single router. Each of them is assigned to a customer; therefore customers can use the same IP (even private IP) with other customers without confusing the PE router. This increases functionality by allowing network paths to be segmented without using multiple devices. Because traffic is automatically segregated, VRF also increases network security and can eliminate the need for encryption and authentication. Internet service providers (ISPs) often take advantage of VRF to create separate virtual private networks (VPNs) for customers; thus the technology is also referred to as VPN routing and forwarding. [boxads]
Logical Router:
VRF acts like a logical router, but while a logical router may include many routing tables, a VRF instance uses only a single routing table. In addition, VRF requires a forwarding table that designates the next hop for each data packet, a list of devices that may be called upon to forward the packet and a set of rules and routing protocols that govern how the packet is forwarded. These tables prevent traffic from being forwarded outside a specific VRF path and also keep out traffic that should remain outside the VRF path.