Juniper Remote Access Configuration
Today i will discuss about Juniper Remote Access Configuration Example. How to enable FTP, SSH, Telnet, http etc…service in Juniper Router/Switch. [boxads]
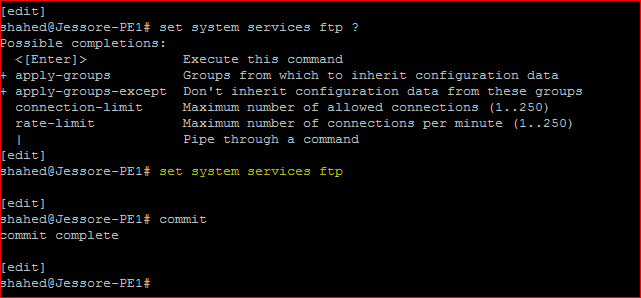
Enable FTP Service:
shahed@Jessore-PE1# set system services ftp ?
Possible completions:
<[Enter]> Execute this command
+ apply-groups Groups from which to inherit configuration data
+ apply-groups-except Don’t inherit configuration data from these groups
connection-limit Maximum number of allowed connections (1..250)
rate-limit Maximum number of connections per minute (1..250)
| Pipe through a command
[edit]
shahed@Jessore-PE1# set system services ftp
[edit]
shahed@Jessore-PE1# commit
commit complete
By default, the router or switch supports a limited number of simultaneous FTP sessions and connection attempts per minute. You can include either or both of the following statements to change the defaults:
- connection-limit limit—Maximum number of simultaneous connections per protocol (IPV4 and IPv6). The range is a value from 1 through 250. The default is 75. When you configure a connection limit, the limit is applicable to the number of sessions per protocol (IPv4 and IPv6). For example, a connection limit of 10 allows 10 IPv6 FTP sessions and 10 IPv4 FTP sessions.
- rate-limit limit—Maximum number of connection attempts accepted per minute (a value from 1 through 250). The default is 150.When you configure a rate limit, the limit is applicable to the number of connection attempts per protocol (IPv4 and IPv6). For example, a rate limit of 10 allows 10 IPv6 FTP session connection attempts and 10 IPv4 FTP session connection attempts.
You can use passive FTP to access devices that accept only passive FTP services. All commands and statements that use FTP also accept passive FTP. Include the ftp statement at the [edit system services] hierarchy level to use either active FTP or passive FTP.
To start a passive FTP session, use pasvftp (instead of ftp ) in the standard FTP format (ftp://destination). For example:
request system software add pasvftp://name.com/jinstall.tgz
You cannot include the ftp statement on routers or switches that run the Junos-FIPS software. We recommend that you do not use the finger service in a Common Criteria environment.
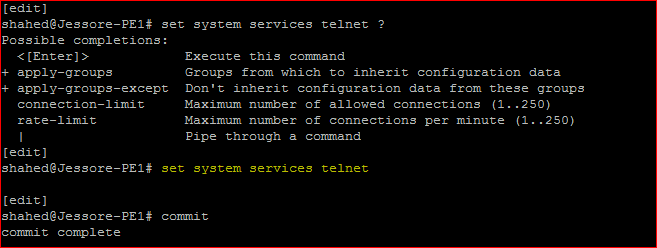
Enable Telent Service:
[edit]
shahed@Jessore-PE1# set system services telnet ?
Possible completions:
<[Enter]> Execute this command
+ apply-groups Groups from which to inherit configuration data
+ apply-groups-except Don’t inherit configuration data from these groups
connection-limit Maximum number of allowed connections (1..250)
rate-limit Maximum number of connections per minute (1..250)
| Pipe through a command
[edit]
shahed@Jessore-PE1# set system services telnet
[edit]
shahed@Jessore-PE1# commit
commit complete
By default, the router or switch supports a limited number of simultaneous Telnet sessions and connection attempts per minute.
Optionally, you can include either or both of the following statements to change the defaults:
- connection-limit limit—Maximum number of simultaneous connections per protocol (IPV4 and IPv6). The range is from 1 through 250. The default is 75. When you configure a connection limit, the limit is applicable to the number of telnet sessions per protocol (IPv4 and IPv6). For example, a connection limit of 10 allows 10 IPv6 telnet sessions and 10 IPv4 telnet sessions.
- rate-limit limit—Maximum number of connection attempts accepted per minute (from 1 through 250). The default is 150. When you configure a rate limit, the limit is applicable to the number of connection attempts per protocol (IPv4 and IPv6). For example, a rate limit of 10 allows 10 IPv6 telnet session connection attempts per minute and 10 IPv4 telnet session connection attempts per minute.
You cannot include the telnet statement on devices that run the Junos-FIPS software. We recommend that you do not use Telnet in a Common Criteria environment.
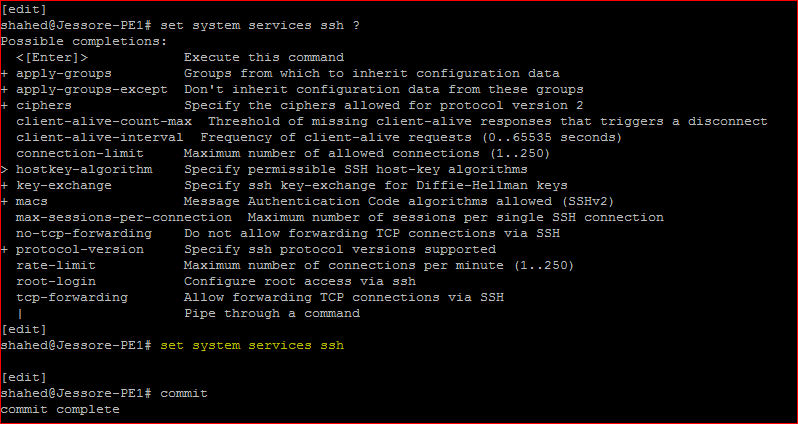
Enable SSH Service:
[edit]
shahed@Jessore-PE1# set system services ssh ?
Possible completions:
<[Enter]> Execute this command
+ apply-groups Groups from which to inherit configuration data
+ apply-groups-except Don’t inherit configuration data from these groups
+ ciphers Specify the ciphers allowed for protocol version 2
client-alive-count-max Threshold of missing client-alive responses that triggers a disconnect
client-alive-interval Frequency of client-alive requests (0..65535 seconds)
connection-limit Maximum number of allowed connections (1..250)
> hostkey-algorithm Specify permissible SSH host-key algorithms
+ key-exchange Specify ssh key-exchange for Diffie-Hellman keys
+ macs Message Authentication Code algorithms allowed (SSHv2)
max-sessions-per-connection Maximum number of sessions per single SSH connection
no-tcp-forwarding Do not allow forwarding TCP connections via SSH
+ protocol-version Specify ssh protocol versions supported
rate-limit Maximum number of connections per minute (1..250)
root-login Configure root access via ssh
tcp-forwarding Allow forwarding TCP connections via SSH
| Pipe through a command
[edit]
shahed@Jessore-PE1# set system services ssh
[edit]
shahed@Jessore-PE1# commit
commit complete
[bodyads]
By default, the router or switch supports a limited number of simultaneous SSH sessions and connection attempts per minute. Use the following statements to change the defaults:
- connection-limit limit—Maximum number of simultaneous connections per protocol (IPV4 and IPv6). The range is a value from 1 through 250. The default is 75. When you configure a connection limit, the limit is applicable to the number of SSH sessions per protocol (IPv4 and IPv6). For example, a connection limit of 10 allows 10 IPv6 SSH sessions and 10 IPv4 SSH sessions.
- max-sessions-per-connection number—Include this statement to specify the maximum number of SSH sessions allowed per single SSH connection. This allows you to limit the number of cloned sessions tunneled within a single SSH connection. The default value is 10.
- rate-limit limit—Maximum number of connection attempts accepted per minute (a value from 1 through 250). The default is 150. When you configure a rate limit, the limit is applicable to the number of connection attempts per protocol (IPv4 and IPv6). For example, a rate limit of 10 allows 10 IPv6 SSH session connection attempts per minute and 10 IPv4 SSH session connection attempts per minute.
By default, a user can create an SSH tunnel over a CLI session to a router running Junos OS via SSH. This type of tunnel could be used to forward TCP traffic, bypassing any firewall filters or ACLs, allowing access to resources beyond the router. Use the no-tcp-forwarding option to prevent a user from creating an SSH tunnel to a router via SSH.
For information about other configuration settings, see the following topics:
- Configuring the Root Login Through SSH
- Configuring the SSH Protocol Version
- Configuring the Client Alive Mechanism
Configuring the Root Login Through SSH
By default, users are allowed to log in to the router or switch as root through SSH. To control user access through SSH, include the root-login statement at the [edit systems services ssh] hierarchy level:
allow—Allows users to log in to the router or switch as root through SSH. The default is allow.
deny—Disables users from logging in to the router or switch as root through SSH.
deny–password—Allows users to log in to the router or switch as root through SSH when the authentication method (for example, RSA) does not require a password.
Configuring the SSH Protocol Version
By default, both version 1 and version 2 of the SSH protocol are enabled. To configure the router or switch to use only version 1 of the SSH protocol, include the protocol-version statement and specify v1 at the [edit system services ssh] hierarchy level:
To configure the router or switch to use only version 2 of the SSH protocol, include the protocol-version statement and specify v2 at the [edit system services ssh] hierarchy level:
To explicitly configure the router or switch to use version 1 and 2 of the SSH protocol, include the protocol-version statement and specify v1 and v2 at the [edit system services ssh] hierarchy level:
For J Series Services Routers, the export license software supports SSH version 1 only.
Configuring the Client Alive Mechanism
The client alive mechanism is valuable when the client or server depends on knowing when a connection has become inactive. It differs from the standard keepalive mechanism because the client alive messages are sent through the encrypted channel. The client alive mechanism is not enabled at default. To enable it, configure the client-alive-count-max and the client-alive-interval. This option applies to SSH protocol version 2 only.
In the following example, unresponsive SSH clients will be disconnected after approximately 100 seconds (20 x 5).
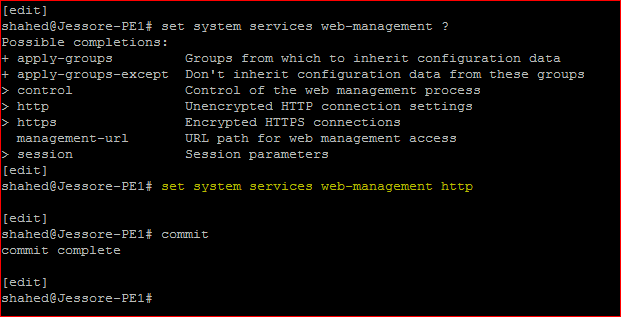
Juniper Remote Access, Enable WEB Service:
[edit]
shahed@Jessore-PE1# set system services web-management ?
Possible completions:
+ apply-groups Groups from which to inherit configuration data
+ apply-groups-except Don’t inherit configuration data from these groups
> control Control of the web management process
> http Unencrypted HTTP connection settings
> https Encrypted HTTPS connections
management-url URL path for web management access
> session Session parameters
[edit]
shahed@Jessore-PE1# set system services web-management http
[edit]
shahed@Jessore-PE1# commit
commit complete